
Cyber-Physical Protection Platforms Safeguard Critical Operations
By coupling threat detection systems with intelligent actions, organizations can better protect their processes from internal and external threats.
By Wayne Cantrell, Siemens Government Technologies
With each passing year, it becomes more common to hear of data breaches and ransomware attacks, often of increasing intensity and impact. Victims shell out great sums of money to take back their systems and data, and valuable user information is compromised.
These incidents have been making headlines in the IT world regularly for quite some time, but they are now affecting operational technology (OT) installations more regularly. Unfortunately, attacks on OT and critical infrastructure are bound to continue because bad actors are realizing the havoc they can wreak by overtaking equipment meant to maintain stable civic life. In the event of an OT cyberattack, the consequences go beyond data loss, potentially compromising workplace safety for operators and employees through runaway equipment, and finished products and services received by consumers.
With focused efforts, it is possible and vital for utilities, manufacturers, and industrial automation users of all kinds to safeguard their facilities and processes from malicious cyber intrusions. This article describes some common—but not entirely effective—efforts for securing OT and critical infrastructure, and then proposes a better strategy to protect systems by utilizing a cyber-physical protection platform.
Network monitoring and threat detection is not enough for OT systems
A 2018 application and network security study by Radware revealed the average cost of a penetrating cyberattack is a staggering $1.1 million. In addition to being a major financial and business continuity disruption, a cyberattack can erode confidence and public trust, critical factors in today’s business landscape.
While network monitoring and artificial intelligence (AI)-driven threat detection systems provide a positive start to cyberattack reduction and mitigation, they do not go far enough to address modern-day cyber threats to OT systems. These software systems are capable of detecting and alerting administrators about suspicious network activity, and in some cases block it, but remediation capabilities are debilitatingly limited.
When a cyberattack gets through, there is not much—if anything—these systems can do to kill the threat and control damage to the OT environment. They typically rely on human intervention to shut off hackers’ connections to the network, and to reclaim machine and process control.
In addition to these shortcomings, threat detection systems often only monitor network traffic at the edge, that is what is coming in and leaving the local network. But OT users are moving to a ‘zero-trust’ stance, recognizing threats do not only come from outside an organization, but can also come from within it. As a result, there is also a need to watch and secure traffic on the local network.
Following an attack and during remediation—when administrators attempt to restore networks and their devices to a normal state—there is a need to quickly determine impacted systems so they can be properly quarantined while non-infected systems are brought back online to continue operations.
Threat detection systems cannot help classify devices’ infection statuses appropriately, adding to the time and difficulty for restoring production. There are better automated solutions to aid in reducing, mitigating the impact of, and responding to cyberattacks.
Cyber-physical systems provide solutions
Network monitoring was created for IT environments, where the chief concern is preventing unauthorized access to information. In such a setting, cutting off intruders’ access to the network and taking devices offline is often a suitable first response to a cyberattack.
OT security, on the other hand, is not as concerned with preventing unauthorized access to information as it is with preventing loss of physical machine and process control. Compromised control comes with varying safety and operational consequences depending on the industry and equipment involved, but maintaining a safe state 24/7 is paramount for all automation and control systems.
For these OT environments where plant and personnel safety are the driving concerns, integrating one or more cyber threat detection tools with PLC logic to act in the event of an attack provides better protection and assurance. This type of cyber-physical incident response solution responds to threat detection by intelligently maintaining uptime of non-infected production cells when possible. It does this by placing infected components into a safe physical state and quarantining them from the rest of the network, and shutting down bad actors’ access into the system.
While many attacks come from outside a local network, an increasing portion originate from within via privileged access. To protect critical production components from both internal and external threats, system architects can place network monitors at individual production cells to trace all traffic to and from the equipment, with PLCs programmed to take appropriate action when attacks are detected (Figure 1).

Figure 1: All network traffic between the IT and OT spaces and within production cells is monitored in this example network architecture, with a cyber-physical incident response solution to safeguard equipment.
Upon detection of a threat, cyber-physical protection platforms follow a custom-defined checklist to place production equipment into a pre-determined protected state—not necessarily ‘off’. Non-impacted equipment groups may continue to run, decreasing operational disruption and speeding up recovery time, while infected equipment is quarantined.
These systems are uniquely programmed to fit their specific facilities’ needs of safeguarding from, detecting, responding to, and recovering from cyberattacks. They employ the encryption capabilities found in many modern PLCs, and they can also utilize firewalls, VPN tunnels, digital I/O, and other means of secure communication between intelligent automation controllers and plant equipment. These secure channels provide maximum situational awareness during an attack, while protecting non-compromised devices from infection.
Not all threats are treated equally. Threat detection devices sit to the side, funneling data and analyzing its contents (Figure 2). When a threat is identified, it gets passed to controllers on the network, along with an assigned priority. High-priority threats may trigger network security configuration changes or physical protection responses, while low-priority threats might just alert plant personnel.
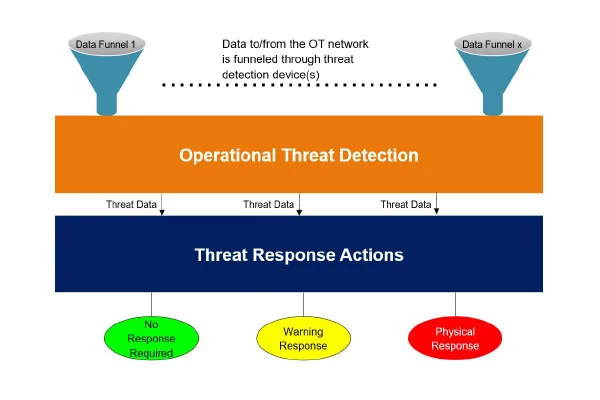
Figure 2: Cyber threat detection solutions funnel network data and send prioritized threats to response PLCs for automated protection sequences.
Cyber-physical protection systems are optimized to analyze threats at OT protocol levels, in legacy and modern environments. They can interact with IT areas and issue immediate responses to protect the OT area when a threat is identified elsewhere on the network. Simultaneous utilization of multiple threat detection solutions increases the probability of attack detection and a quick mitigating response prior to sustaining damage.
Application examples
In addition to the protocol-specific monitoring of OT threat detection software, cyber-physical protection platforms provide suitable responses to a host of threat scenarios specific to particular industries or facilities.
These responses can occur at the network or physical level, manipulating equipment states to maintain safety, which is not necessarily ‘disconnected’ or ‘off’. The following are example applications, describing how a cyber-physical solution could respond to a high-priority threat and manage the attack:
- When an outside intruder attempts to raise a chemical injection setpoint beyond its threshold at a water treatment plant, detection of the intrusion locks the injection pump at its last acceptable dose and alerts operators.
- At a naval yard, an entirely compromised network triggers emergency cooling and enables backup control systems.
- In a beverage plant with five filling lines, the production cell monitoring equipment identifies two are compromised. PLCs shut down equipment on these lines, while network equipment quarantines devices on these lines. The other three lines continue running to maintain uptime and maximize production.
- In response to threat detection at a power plant, circuit breakers are placed in a local mode to prevent malware from operating them over the network. Plant personnel can control the breakers on site from their front panels.
- Within prisons, embassies, and other secure facilities, a network breach invokes physical protection systems to prevent egress.
- A logic or firmware change is detected in a pharmaceutical manufacturing plant, and the cyber-physical protection system issues an immediate production and shipping halt to prevent unvalidated product from entering the marketplace.
Threat detection and response in action
Plants and facilities can utilize Siemens SIBERprotect (patent pending) cyber-physical incident response solution to reduce the risk and consequence of cyberattacks on their OT networks (Figure 3) The installation utilizes a Siemens Ruggedcom switch with a Fortinet Next-Generation Firewall and Nozomi Intrusion Detection System, or similar devices depending on the specific needs.
Less than a second after detecting a threat, the system issues a physical notification via lights and sirens, with a configurable digital notification triggered through the facility’s alarm notification pipeline. Simultaneously, a Siemens S7-1500 cyber response PLC activates a firewall rule change in the SCALANCE industrial security switch, quarantining the production cell equipment. The PLC also deenergizes physical network segmentation hubs to protect legacy equipment on the plant floor, and it issues protection signals to plant equipment, enabling non-impacted lines to continue production.
This system provides the choice between rule-based automatic responses or manual activation of physical safeguards by the facility’s security officers, and it enables triaged remediation of cyberattacks by providing human-decipherable diagnostics for network threats and activity.

Figure 3: The Siemens SIBERprotect cyber-physical incident response solution enables automatic physical responses to and instant notification of network intrusions and unauthorized meddling.
In a case study, SIBERprotect was applied to an operation impacted by the WannaCry ransomware attack of 2017 (Figure 4). Models predict installing a cyber-physical incident response solution could have prevented the impact or reduced the remediation time by up to 99.6 percent, since the attack was not a zero-day exploit.
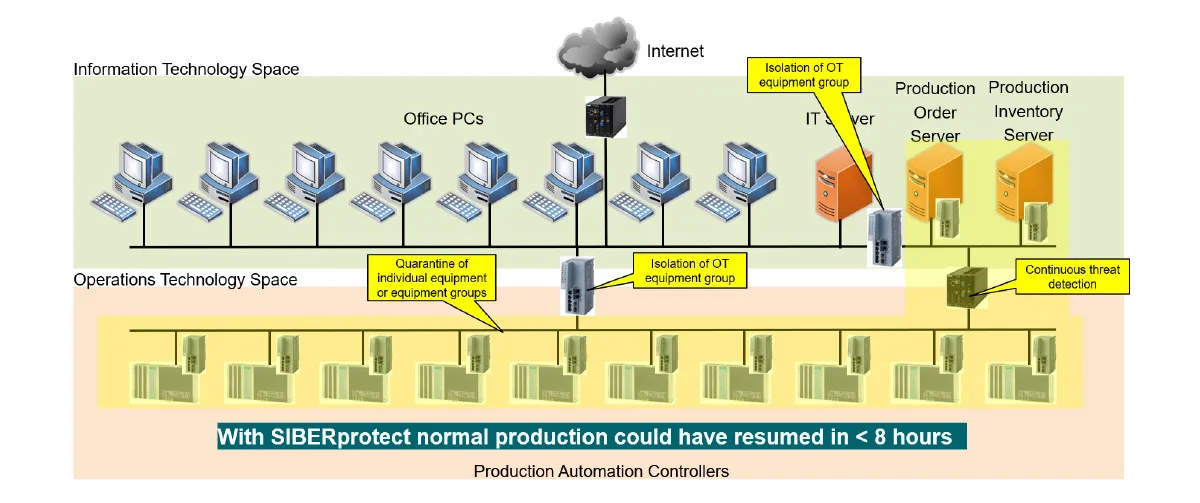
Figure 4: It took a manufacturing facility significantly impacted by the WannaCry ransomware attack of 2017 an estimated two thousand hours to remediate their systems. With a cyber-physical incident response solution in place, it would have taken less than eight.
As the ransomware ran its course, it affected multiple automation controllers, requiring an estimated 2,000 hours of staff and contractor time to remediate before returning the site to a normal operating state. As the remediation effort progressed, several devices ceased operating multiple times due to the difficulty of isolating the malware. An expert assessment after recovery estimated a cyber-physical protection platform would have either prevented the event, or in the worst case kept the OT infection confined to two servers only, requiring eight hours to rebuild and restore to normal operation.
A solution for every plant and facility
Dependable cyber protection cannot be realized overnight because systems must be fitted to facilities’ and industries’ unique requirements. Although there is no one-size-fits-all solution, OT security experts specialize in assisting plants and facilities to define and configure the equipment safe states and automation device communications required to physically protect critical equipment.
There are many IT-specialized threat detection systems on the market, but OT systems carry different requirements. Suitable OT cyber protection solutions must be able to detect network intrusion over industrial protocols, and the best integrate with real-time OT control systems. A complete cyber-physical incident response solution helps users identify and detect threats, protect equipment, manage and respond to breaches, and recover quickly from attacks.
All figures courtesy of Siemens

About the Author
Wayne Cantrell is a senior principal systems engineer with Siemens Government Technologies. He has 39 years of experience in factory automation, process automation, and operational technology cyber security across a wide range of industrial and government OT spaces.
---
1 https://www.radware.com/ert-report-2018